Authentication, Identification, and Authorization for Freshers
Authentication, Identification, and Authorization for Freshers. Enhance protection and control with essential security principles.
As your application gets bigger, there are important things to keep in mind. Make sure it can handle more users and features by scaling it up. Keep it running smoothly and fast by optimizing its performance. Protect user information by adding strong security measures. And don't forget to make it easy and enjoyable for people to use. By considering these things, your application will be able to grow and succeed.
Some of such aspects we are going to cover in this article via a story. So lock in your chair, keep your back start, and start reading…….
Explaining Authentication, Identification, and Authorisation in a unique way through a story.
Background
Once upon a time, there was a huge Kingdom named Nullfort. That kingdom had 4 major responsibilities for the well-being of people.
managing infrastructure
maintaining law & justice
conducting trade and
defending from external threats
In the Kingdom of Nullfort, there was a clear hierarchy that helped in the smooth functioning of the kingdom.
King/Emperor
Nobels/Council members
Knights/Workers
Farmers
In detail:
One King named James was responsible for the overall administration
To assist, Four council members were managing each department and making sure everything is going well.
20 dedicated Workers divided among departments for execution purposes. These workers executed the tasks and projects assigned to them by the council members
The farmers, or peasants, formed a vital part of the kingdom as they were directly affected by the policies and decisions made by the king and council members. They were cultivating the land and providing food for the entire kingdom.
Story
Except for Farmers/Peasants, everyone was working in the castle, roles are divided among council members and workers based on their skills. Everyone was doing their job perfectly
Kingdom Nullfort was running well, with zero issues, 100% efficiency, profitable, and everyone was happy. This made King James proud of all the council members and workers.
Part 1: Authentication
One late night, King James was mesmerized by the starry sky when he noticed two farmers secretly leaving the castle. The very next morning, King James called the council and the two farmers for a crucial meeting. On Investigation, he found the farmers used to enter the castle at night to manipulate the merchant trade rates to earn extra profit leading to a direct loss to the kingdom.
This was a breach in the Kingdom as only Council 3 and King James should be allowed to update the merchant trade rates.
Althought Farmers are part of Kingdom, they should not be allowed to enter the castle as it contains critical information about finance, defense, justice, infrastructure, and public welfare.
Considering Farmers as Unauthorised Users.
Wrt Software, such a case is known as Unauthorised access.
Without authentication, anyone could potentially access sensitive information or perform actions meant for authorized users only. This could lead to unauthorized users gaining control over user accounts, manipulating data, or exploiting system vulnerabilities.
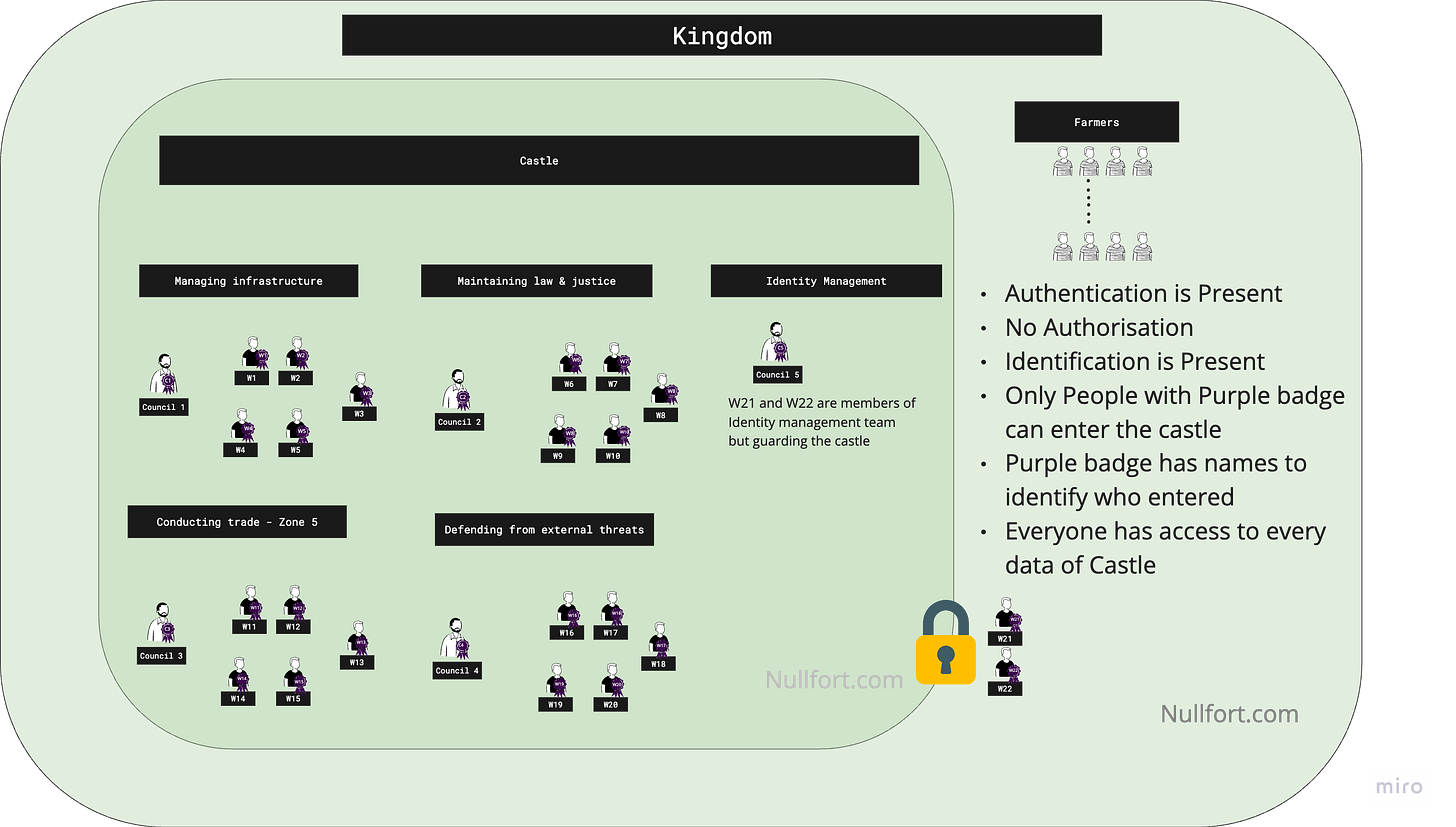
The same week, Kings James formed a new team “Identity Management“ comprising workers W21 & W22, along with one council member C5.
Team Identity Management will be responsible for checking if the user entering the castle should be either a King Council member or a worker. For authentication, they were given badges of Purple color with the Kingdom mark.
Wrt Software, the purple badge was like the credential or token
Authentication is a process that confirms the identity of a user by validating their credentials through various mechanisms, such as passwords, biometrics, or security tokens, to ensure authorized access to a system or application.
From there on, W21 and W22 allow entry only to members who have a purple badge.
Wrt Software, Authentication is performed by backend libraries, which verify user identity through methods like username/password validation, integration with external providers, or the use of biometric data to grant or deny system access.
In the above story, the castle is the system while W21 and W22 are the backend libraries.
King James was too happy that all the data inside the castle is now secured as entry to Farmers is now restricted.
Part 2: Identification
Now any person with the purple badge is allowed into the castle. Workers W21 and W22 were only able to keep count of the number of people who are entering the castle.
Worker W21 noticed that the number of people entering the building is too large in one day than the actual badges issued. After raising it with King James, names were written on all the badges.
Due to names written on badges, every badge is now unique and Worker 21 & worker 22 are able to track who is entering the building. Wrt above issue, it was found that workers W12 and W14 were leaving the castle multiple times for taking breaks.
Identification is the process of confirming someone's identity through personal information or documents. It helps establish who a person is in a reliable and verifiable manner.
In the above text, personal information is the name written on the badge
Difference between Authentication and Identification wrt story
Identification is about assigning unique badges or credentials to individuals, while authentication ensures those badges are valid and match the claimed identity.
Part 3: Authorization
King James was satisfied that all the critical information inside the castle is now protected from farmers and we can track who is entering and exiting the castle.
A few months passed, and Monsoon season was approaching soon. King James realized it is the right time to start maintaining of all the roads of the Kingdom.
Council member C1 came up with the budget for all the road maintenance which was a secret from road contractor and Kingdom. Only council members C1 and King James should be aware of the budget.
King James called road contractor Zen who has been managing roads of Kingdom Nullfort from past few years
King James wanted to negotiage with contractor Zen on price much lower than secret Budget. However somehow contractor Zen was aware of the budget and was not ready to negotiate.
He aborted the negotiation and started the investigation with Zen and within the kingdom. Post investigation, they found Workers W12 and W14 were bribed by road contractors and they had leaked the budget after accessing the secret budget file.
King James ordered Council member C5(“Identity Management“ ) to come up with a solution.
Council member C5 stated, “Like we are allowing limited access inside the castle, we have to implement similar security with all the resources of the castle“.
King James questioned, “You mean we have to give more badges to the people for each resource?“
Council member C5 replied “No, we have to mention on the batch what access user has inside the castle“ and for accessing it user has to be inside the castle as…
Authentication is a prerequisite for authorization (as users must be authenticated before their access can be determined)
King James was confused and gave Council member C5 one month to implement the solution. Council member C5 created multiple locker rooms inside the castle. Multiple workers were hired called Wn to gate each locker room.
Along with that, Council member C5 updated all the badges with list of locker rooms a particlular worker or council member is allowed. Ofcourse King James’s purple badge had access to all the locker rooms.
These locker room contains all the information related to the particluar department and only certain people were allowed to enter based on the list of locker rooms present on their purple badge.
Example:
Locker room 1 → “Managing Infrastructure Locker“
Access was limited to Council member C1, Workers W1, W2, W3, W4
Locker room 2 → “Managing Infrastructure Locker Admin“
Access was limited to Council member C1
Once all the badges were updated and locker rooms were ready. King James was ready to start the road construction process. Council member C1 came up with new budget and Road constructor Zen was called for negotiation. This time since data was present in Locker room 2, Zen was failed to bribe any of the worker.
Negotiation was done and Zen agreed for road maintainance contract in half of the budget price. This way Kingdom saved fifty percent of the budget which can be reused in other forms
Mentioning list of locker rooms on purple badge of every user is similar to Authorization to user in software. Wrt Software, we link permissions/roles to every user.
Authorization is the process of granting or denying access rights and permissions to authenticated users based on their roles, privileges, or specific permissions assigned to them.
King James was happy with the "Identity Management" team for their successful implementation of the authentication, authorization, and identification processes.
These incidents served as a valuable lesson for the kingdom, highlighting the importance of maintaining a robust authorization system and remaining vigilant against potential breaches. The people of Nullfort could once again sleep peacefully, knowing that their Kingdom’s information was safeguarded by a fortified authorization system that had learned from its past vulnerabilities.